Most organisations treat their ISMS as an ISO 27001 compliance exercise, policies, procedures, and evidence artefacts assembled to satisfy auditors. The certificate goes on the wall. The management review happens annually. The risk register gets updated before surveillance audits.
This misses the point entirely. An ISMS is a management system. Built properly, it drives security decisions, allocates resources to actual risk, and provides the organisation with genuine visibility into its security posture. Built for compliance, it produces documentation that satisfies auditors whilst security decisions continue to be made informally, inconsistently, and without accountability.
I publish this framework because transparency builds trust. This is the methodology I apply in advisory engagements — adapted to each organisation’s context, maturity, and risk profile. The published version demonstrates the approach; the engagement delivers the application.
The core ISMS capabilities
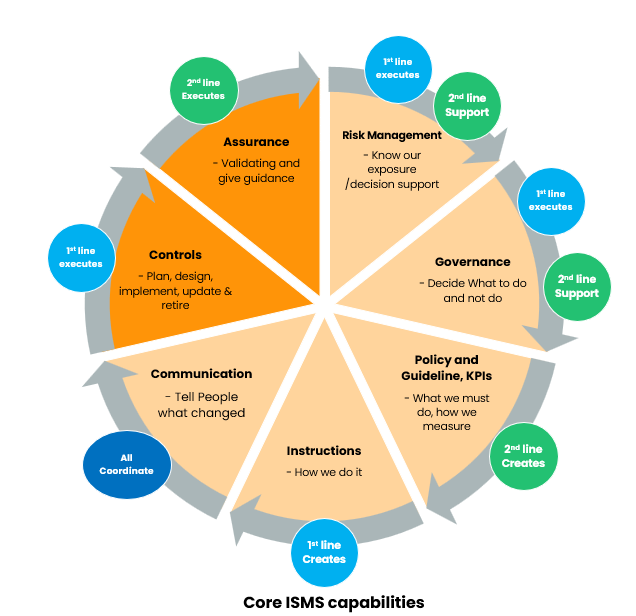
The capability wheel maps seven areas that an ISMS must address to deliver real security value. Each operates across the three lines model and none stands alone:
- Risk Management: know our exposure. Decision support for the business, not a compliance artefact.
- Governance: decide what to do and not do. Accountability structures that make real decisions.
- Policy and Guideline, KPIs: what we must do, how we measure. The documented expectations and the evidence they’re met.
- Instructions: how we do it. Operational procedures that translate requirements into daily practice.
- Communication: tell people what changed. Strategic, tactical, and operational information flows.
- Controls: plan, design, implement, update and retire. The measures that actually reduce risk.
- Assurance: validating and giving guidance. Systematic evidence that the system works.
These capabilities overlap and reinforce each other. A control without a policy basis lacks authority. A KPI without governance context measures the wrong thing. Risk management without communication produces assessments nobody acts on. Instructions without controls lack rationale. Governance without risk input makes decisions in the dark.
The portfolio sections below explore each capability from a practical perspective: what the typical state looks like, why it goes wrong, and what good practice actually requires.
For the full argument on why this matters now, and a side-by-side comparison of compliance-driven vs risk-based ISMS practice, read The ISMS beyond the certificate.
Cross-cutting series
System Security Concepts
A 7-article series on implementing systematic security documentation within ISMS frameworks. Security concepts cut across multiple capabilities. They are controls (ensuring security is designed in), communication instruments (connecting stakeholder perspectives), and assurance foundations (providing evidence for validation). Published January 2026.
If this framework resonates with challenges in your organisation, get in touch.